Amazon Quietly Patched an Alexa Hacking Vulnerability Discovered by Cybersecurity Researchers in June
Hackers could trick Amazon’s Alexa voice assistant into giving away personal information and accept commands from unauthorized users, according to a new report from cybersecurity provider Check Point. Amazon patched the problem in June when Check Point notified the company about the potential issue, but fixing this vulnerability doesn’t eliminate the possibility of others. The discovery only reinforces why Amazon and other voice assistant developers continue to highlight their privacy and security measures, especially when both are frequently cited as reasons people avoid buying smart speakers and other voice-enabled devices.
False ID
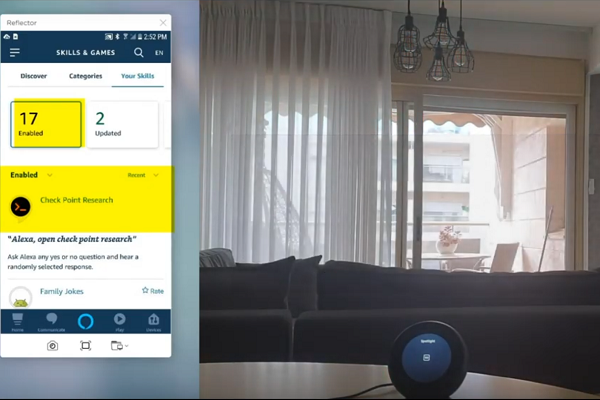
Check Point found and exploited the vulnerability through the Alexa smartphone app. The researchers essentially fooled the software into not examining network traffic, allowing them to replace a real app owner with a fake linked to malicious code. Once the real user unwittingly clicked on the link, it would open a door for the researchers to take over the account. The hacker could then add and remove Alexa skills, view their history of voice commands, and leverage information on the account for other identity hacks or blackmail attempts. You can see a demonstration in the video above, set to slightly over-the-top suspenseful music. The maneuver’s technical complexity eliminated any concern about people accidentally using this trick to access someone else’s account, but there’s an eternal specter of people with more ability than ethics figuring out how to do what Check Point did. The researchers tagged the Internet of Things and smart devices as needing better protection from these kinds of hacks
“As virtual assistants today serve as entry points to people’s home appliances and device controllers, securing these points has become critical, with maintaining the user’s privacy being top priority. This was our “entry point” and central motivation while conducting this research,: Check Point explained in the new paper. “Successful exploitation would have required just one click on an Amazon link that has been specially crafted by the attacker.”
Securing Alexa
Check Point told Amazon what it had found in June but presumably held back the public report in part to give Amazon time to close the loophole. Amazon did so once it knew about the problem and said in a statement that it doesn’t know of anyone using this hack against customers, although it appreciates the work of Check Point and other white hat hackers. Like its rivals, Amazon’s security policy for third-party IoT devices has grown stricter. Earlier this year, Amazon tightened the minimum security requirements for using Alexa Voice Service (AVS). The mix of hardware and software requirements, as well as security maintenance checks, are aimed at limiting the chance that unauthorized users will take over an account in a way similar to what Check Pont found.
Alexa has been pretty responsive to these kinds of reports. When Security Research Labs (SR Labs) told Amazon and Google about some security vulnerabilities in Alexa skills and Google Actions, Amazon quietly resolved the issue, while Google’s process removed thousands of Actions worldwide for several days without any warning. The preemptive blocking of hackers is certainly preferable to dealing with scam artists and hackers exploiting Alexa users. Amazon is in the midst of a lawsuit against companies for an Alexa tech support fraud scheme that tricks people into thinking the scammers are affiliated with Alexa using fake setup apps to extort money from customers. On the other hand, voice assistant users probably don’t need to worry about any lasers hacking their smart speaker.
Follow @voicebotai Follow @erichschwartz