Nyansa Launches Voyance IoT, a Platform to Monitor the Security of Enterprise IoT Devices

Image Credit: Business Insider
Yesterday Nyansa unveiled Voyance IoT, an AI-based solution to integrate IoT security and device performance analytics within a single platform. Voyance IoT will automatically classify, secure, and analyze the behavior of IoT devices from end-to-end across enterprise wired and wireless access networks. Nyansa was founded in 2013 and is credited with developing the first cloud-based network analytics system, called Voyance. The company has raised $26.5 million to date.
Nyansa Is Tackling the Current and Future Use of IoT Devices
Nyansa saw an opportunity to pursue the security of IoT devices, a market which is rapidly growing. According to IoT Analytics, the number of IoT devices in August 2018 was at 7 billion. In addition, the company predicted that by 2025 there would be 21.5 billion total active device connections worldwide.
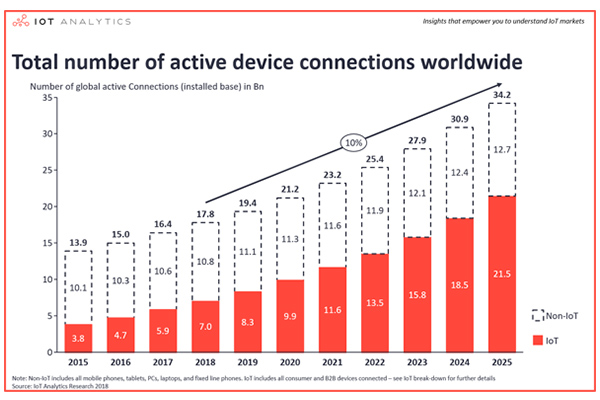
Image Credit: IoT Analytics
Nyansa boasts a powerhouse team, the company website states
We dig data, I mean REALLY dig. It’s as simple as that. We have a bunch of PhDs from MIT, and MBA types from Harvard, Cisco/Meraki, Aruba Networks, Google guys and so on and so forth. And we’re as diverse as diverse gets. Despite all that, our geeks know how to code, right, the first time, every time. And it shows. We hope.
CEO and co-founder, Abe Ankumah, has had a career in the front-row seat of IT trends, from developing satellite software for NASA, building chips for a startup that has since been acquired from Intel, and then heading cloud networking at Cisco’s Meraki. For Ankumah, seeing the rise of the Internet of Things is one of the biggest changes he has witnessed and is what prompted him to leave Cisco to start Nyansa in 2013. What inspired Nyansa to create the Voyance IoT software was talking to customers. Ankumah says,
With companies increasingly using connected devices, this increases the attack surface — meaning there are more opportunities for a hacker to extract data. And in many cases, security is only built into a device as an afterthought.
Voyance IoT Specs
Voyance IoT will allow consumers to make sure all of their devices are working properly and to help address potential security vulnerabilities by using artificial intelligence. The software will classify, secure, and analyze the behavior of IoT devices as it is able to see what exactly the devices are “talking to” on a network. For example, if a device on a company’s network is talking to another device on that network as planned, Voyance IoT can see that everything is normal. However, if a device starts talking to an unknown device in an unexpected location, like Russia, Voyance IoT will alert users.
Not only is connecting to unknown devices a common problem Voyance IoT aims to fix, but there is also a problem of finding connected devices on networks when they should not be there. Nyansa CTO and co-founder Anand Srinivas says he has seen this issue in hospitals and retail. Certain devices in hospitals should be on secure networks because they collect sensitive patient data, like an X-ray or electrocardiogram machine. But Srinivas says he has seen smart TVs and even cars connected to those networks. Srivanas told Business Insider,
When it talks to the network, every time it talks, who is it talking to? That’s the data we’re collecting. You see the weirdest devices.
Nyansa Works to Fix Well Known Problems
Other people feel similarly to Nyansa. In December 2018, Brent Scott wrote in Voicebot.ai about IoT products and the undeniable reality that they will need more security features. McAfee released a Labs 2019 Threats Prediction Report in early December 2018, detailing seven different security threat predictions. The report stated that the cloud will be the main target of security threats and also stated that voice assistants on mobile devices will act as the “picklock” to a much larger door.
Smartphones provide access to voice assistant apps, which can hold personal data ranging from simple alarms to banking information. The McAfee report hit on a very important point: voice assistants are such a target because they act as the hub for smart home devices.
The real key to the network door next year will be the voice-controlled digital assistant, a device created in part to manage all the IoT devices within a home.
Existing examples of cybercriminals exploiting unprotected devices include the Mirai botnet and the IoT_reaper. Consider the negative consumer reaction to finding out that the Nest IoT Security Hub included a microphone only when it became Google Assistant enabled. Not only were consumers upset by the realization, but the Senate Commerce Committee sent a letter to Google CEO Sundar Pichai about the news reports that its Nest Guard IoT security hub included an onboard microphone but didn’t inform customers of its presence. One of the most well-known examples of IoT devices being hijacked may be the hacking of baby monitors.
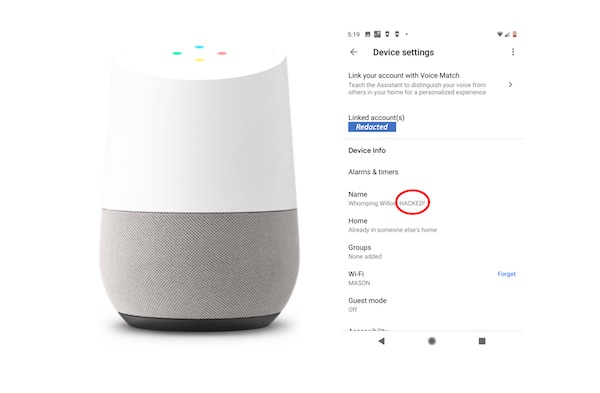
Consider a Voicebot exclusive from last week on Google Home user data able to be seen on shared WiFi Networks. Voicebot was contacted by Assistant Professor of Information Systems and Operations Management at the George Mason University School of Business, Belal Abdelfattah, who said his Google Home Mini began playing loud music without him prompting the device. The incident led him to find that information on more than a dozen other Google Home devices all on the University’s shared network were available to him using the Google Home app. The information available included the device name, the device owner’s name, and what content was streaming. In addition, Abdelfattah found that he could actually change the device name, stream music to the other devices, reboot them and control the volume. When asked about Abdelfattah’s findings, a Google spokesperson responded by saying that Google Home is meant for home networks, not public ones.
Nyansa’s method of monitoring IoT device activity includes monitoring smart speaker activity. In the case of the Google Home Mini, it could aid Universities and offices in protecting their smart speakers. The development of a tool like Voyance IoT highlights the very real security risks of using IoT devices but the questions remains if enterprises and consumers feel that the threat is enough to buy a solution for the problem.
Sensory is Enabling Offline Smart Speakers with No Cloud Connectivity to Maximize Security