Google Home Location Security Vulnerability to be Closed in July
A security researcher from Tripwire, Craig Young, has determined that a feature common to Google Home and Chromecast can enable someone to remotely determine a user’s precise location. The concern is that by simply visiting a website and clicking on a certain content link, the browser’s HTLM5 location tools can be used in conjunction with Google’s location services to accurately identify a person’s location within a few meters. IP location might track you within a few miles. As a result, by visiting a compromised website a hacker could determine your precise home address simply by querying what Google devices are on your network.
Your Location within 10 Meters By Simply Visiting a Website
The concern is that hackers could use this information in extortion schemes by appearing more credible and being able to identify seemingly anonymous website visitors by their home addresses. Brian Krebs of KrebsOnSecurity notes:
“It is common for Web sites to keep a record of the numeric Internet Protocol (IP) address of all visitors, and those addresses can be used in combination with online geolocation tools to glean information about each visitor’s hometown or region. But this type of location information is often quite imprecise. In many cases, IP geolocation offers only a general idea of where the IP address may be based geographically.
“This is typically not the case with Google’s geolocation data, which includes comprehensive maps of wireless network names around the world, linking each individual Wi-Fi network to a corresponding physical location. Armed with this data, Google can very often determine a user’s location to within a few feet (particularly in densely populated areas), by triangulating the user between several nearby mapped Wi-Fi access points.”
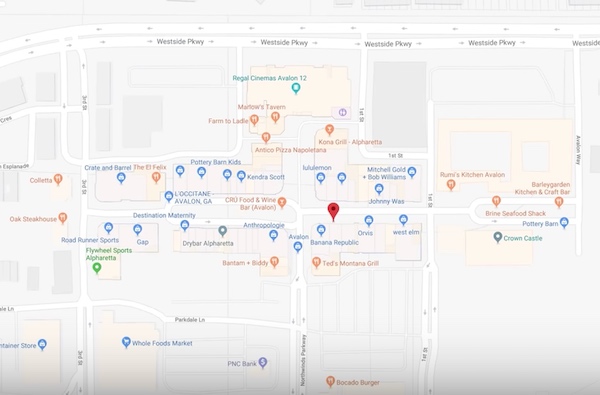
Young also told Krebs that in his demo he has consistently been able to find locations within about 10 meters of a device and that each of the three environments he has tested resulted in obtaining a correct street address. He even found the information to be accurate enough in his own home to determine, “roughly how far apart his device in the kitchen is from another device in the basement.” The video below shows how Young started as a guest browsing a website and the data generated from his session allowed for the street location of his address to be revealed.
A Low Friction Feature is Also a Bug
The problem arises from a feature Google implemented to reduce friction in on-boarding devices to a local network and for Google devices to automatically discover each other. This makes it easier for user set-up and access features that enable Google devices to work together such as asking Google Home to start a YouTube video using Chromecast. Young says this low-friction approach also introduces the security vulnerability and stems from two design choices that are common among IoT devices:
- Devices rarely require authentication for connections received on a local network
- HTTP is frequently used to configure or control embedded devices
“The confluence of these properties means that web browsers and, therefore, websites can sometimes interact with network devices.” Young also says that this information could be used by advertisers along with other web activity to determine a website visitor’s identity.
“Browser extensions and mobile apps can use their unrestricted network access to directly query the devices without relying on or waiting for a DNS cache refresh. This gives advertisers a direct path to obtain location data without alerting the end-user. The location data can then be correlated with other tracked web activity and possibly tied to a specific real-world identity. This gives advertisers a direct path to obtain location data without alerting the end-user. The location data can then be correlated with other tracked web activity and possibly tied to a specific real-world identity.”
Google to Address the Issue
Young told Krebs that his first attempt to have Google address this issue in May was rebuffed. The response to his bug report was a “Status: Won’t Fix (Intended Behavior)” message. After being contacted by KrebsOnSecurity, Google changed its position and said there will be an update shipped in “mid-July 2018.”
This situation highlights the fundamental conflict between features that enable ease of use and those that attempt to protect privacy and security. It is inconvenient to have passwords to dozens of websites but doing so typically provides a modicum of security protection. It is even more inconvenient to use a VPN, but the fully encrypted traffic protects users from having their data communications revealed to outsiders. Similarly, it is inconvenient to force each device to discover other devices on a home network which is assumed to be populated with only friendly devices. This permissive behavior helps consumers while also introducing risk.
Permissiveness is More Convenient but Introduces Risk
Voice assistants and smart speakers in general face the same trade-offs. A more permissive smart speaker wouldn’t require a wake word at all. It would always listen and know when to respond automatically. I saw this demonstrated at CES by Nuance in an automobile. That implementation reduces friction for the user but involves the system to always listen for a much broader set of language which introduces privacy concerns. You can understand why Google’s initial reaction was that the protocols were “intended behavior” and didn’t need to be addressed. The permissiveness of the devices offer benefits to users.
However, on reflection, Google didn’t want to be viewed as introducing a security vulnerability into the home. It doesn’t want to introduce any reasons for consumers to be cautious about adopting Google Home smart speakers or other Google devices. What will be interesting is whether the fix makes it harder to use Google devices in coordination and more difficult to join a WiFi network.
It is worth noting that Amazon faced a similar issue recently with its Echo smart speakers that it quickly addressed. A security researcher determined how to keep the microphone open and capture a transcript of up to 16 seconds of speech without notifying the user. This was the result of some features for developers being misused that were originally intended to offer more options for enabling the user experience. The exploit was eliminated by Amazon shortly before it was made public by the researcher. However, there will be more of these. Smart speakers are now popular and in many homes. That makes them a good target for security researchers to try and compromise for the PR value and for hackers considering new ways to launch attacks.
Sensory Announces Updated Voice Security with TrulySecure Speaker Verification 2.0